
Learn how to achieve security compliance in sensor-based systems with key standards like IEC 62443, Southeast Asian mandates, and a practical step-by-step framework.

Security compliance in sensing systems: a step-by-step guide

TL;DR:
- Sensor-based systems require specific compliance with international, regional, and industry standards due to OT-IT convergence.
- Regional mandates in Southeast Asia, such as Vietnam's QCVN 135 and Singapore's CSA advisories, impose strict security controls on sensors.
- Adopting a risk-based, OT-focused approach with thorough asset management and zone modeling ensures effective compliance.
Most security managers assume that if their IT infrastructure passes a compliance audit, their sensor-based systems are covered too. That assumption is costly. Sensor-based systems sit at the intersection of operational technology (OT) and IT, creating a compliance gap that standard IT frameworks were never designed to close. Across Southeast Asia, new mandates from Vietnam and Singapore are raising the bar, and government agencies and industrial facilities that haven't aligned with both international standards and local regulations face real operational and regulatory exposure. This guide maps the key frameworks, regional requirements, and a practical step-by-step approach to get your sensing systems fully compliant.
Table of Contents
- Understanding security compliance in sensor-based systems
- Core standards and frameworks for compliance
- Regional mandates and Southeast Asian regulatory trends
- Step-by-step approach to security compliance for sensing systems
- Common challenges and practical solutions
- Why risk-based, OT-focused compliance trumps IT-first approaches
- How BeyondSensor helps you achieve compliance with confidence
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| OT-specific compliance is critical | Standards like IEC 62443 and NIST SP 800-82 are essential for sensor-based system security. |
| Local regulations impact compliance | Singapore and Vietnam enforce specific requirements for sensor-based security systems starting in 2026. |
| Risk-based approach wins | Tailoring compliance strategies to your operational technology and local context outperforms one-size-fits-all IT strategies. |
| Operational process matters | A stepwise method involving inventory, segmentation, defense-in-depth, and documentation supports sustained compliance. |
Understanding security compliance in sensor-based systems
Security compliance in sensor-based environments is not simply about firewalls and patch management. It means meeting a layered set of international, regional, and industry-specific standards that address the unique risks of OT environments, where availability and physical safety often matter more than data confidentiality.
Understanding why security compliance matters for sensing systems starts with recognizing how different they are from traditional IT assets. Sensors in industrial or government facilities control physical processes, monitor perimeters, and feed data into SCADA and distributed control systems. A misconfigured sensor is not just a data risk. It can mean a failed alarm, a missed intrusion, or a safety incident.
Key frameworks that apply to these environments include:
- IEC 62443: The primary international standard for cybersecurity in industrial automation and control systems (IACS), including sensor-based systems
- NIST SP 800-82: Provides guidance for securing ICS, including sensors in SCADA and distributed control systems
- CISA Cybersecurity Performance Goals (CPGs): Baseline cross-sector practices applicable to sensor environments
- Local mandates: Singapore's CSA advisories and Vietnam's QCVN 135:2024/BTTTT for IP cameras and sensors
What makes compliance genuinely complex is the convergence layer. Sensor systems use both IT protocols (TCP/IP, MQTT) and OT protocols (Modbus, DNP3), meaning cybersecurity standards for device security must address both worlds simultaneously.
"Treating sensor-based OT systems as if they were standard IT endpoints is one of the most common and dangerous compliance mistakes we see in industrial facilities across the region."
Pro Tip: Start your compliance journey by classifying every sensor as either an IT asset, an OT asset, or a hybrid. This single step clarifies which standards apply and prevents you from applying the wrong controls to the wrong systems.
Core standards and frameworks for compliance
Having defined compliance, it's crucial to map the specific frameworks that shape requirements and how they interplay with each other.
IEC 62443 defines 7 Foundational Requirements and 4 Security Levels (SL 0 through SL 4), allowing you to calibrate protection intensity based on the consequence of a breach. A perimeter sensor at a water treatment plant may require SL 3, while an indoor motion detector in a low-risk office might sit at SL 1. This tiered model is what makes IEC 62443 so well suited to industrial sensing environments.
NIST SP 800-82 complements IEC 62443 by providing ICS-specific controls covering network segmentation, access management, and risk assessment processes. It is especially useful for facilities that must align with U.S. federal procurement requirements or work with American technology partners.
The CISA CPG Report 2.0 outlines 37+ baseline practices applicable to sensor systems, covering asset inventory, incident response, and governance. These are practical, actionable, and designed to be achievable even for organizations early in their compliance journey.
| Standard | Primary focus | Security levels/tiers | Key coverage |
|---|---|---|---|
| IEC 62443 | OT/IACS cybersecurity | SL 0 to SL 4 | Zone/conduit model, foundational requirements |
| NIST SP 800-82 | ICS risk management | Low/Moderate/High | Network segmentation, access control, risk assessment |
| CISA CPGs | Cross-sector baseline | Not tiered | Asset inventory, incident response, governance |
| EN 18031 | Internet-connected devices | Not tiered | Encryption, authentication for EU-connected sensors |
For multinationals operating in both Southeast Asia and Europe, EN 18031 adds specialized requirements for internet-connected sensors. Aligning with physical security compliance standards across all applicable frameworks early prevents costly retrofits later.
- IEC 62443: Best for industrial automation, perimeter detection, and SCADA-connected sensors
- NIST SP 800-82: Best for facilities with U.S. government contracts or American technology stacks
- CISA CPGs: Best as a practical starting checklist for any organization
- EN 18031: Required for sensors that connect to EU cloud infrastructure or serve European clients
Regional mandates and Southeast Asian regulatory trends
Global frameworks are only half of the equation. Let's look at the regulatory landscape within Southeast Asia itself.
Vietnam's QCVN 135:2024/BTTTT mandates 11 security requirements for IP cameras and sensors, effective from 2026. These include encryption of data in transit, unique default passwords, firmware integrity verification, and vulnerability disclosure obligations. Any facility deploying networked sensors in Vietnam must ensure their hardware and software vendors meet these requirements before procurement.
Singapore's Cyber Security Agency (CSA) recommends ICS/SIS protection through network segmentation and strict access controls. Singapore-based critical infrastructure operators, including those in energy, water, and transportation, are expected to align with these advisories as part of their Critical Information Infrastructure (CII) obligations.
| Country | Key regulation | Effective date | Core requirements |
|---|---|---|---|
| Vietnam | QCVN 135:2024/BTTTT | 2026 | Encryption, unique passwords, firmware integrity |
| Singapore | CSA ICS Advisory | Active | Segmentation, access control, incident reporting |
| Regional (ASEAN) | ASEAN Cybersecurity Framework | Ongoing | Baseline harmonization across member states |
For facilities managing infrastructure security safeguards, the key compliance actions include:
- Auditing all IP cameras and networked sensors against QCVN 135 requirements before 2026 deadlines
- Implementing network segmentation between sensor networks and corporate IT
- Establishing documented access control policies for all OT/sensor systems
- Aligning procurement specifications with both local and international standards
Pro Tip: If your organization operates across multiple Southeast Asian countries, map each local regulation against IEC 62443 requirements. Most local mandates overlap significantly with IEC 62443's foundational requirements, so a single compliance program can satisfy both with targeted additions.
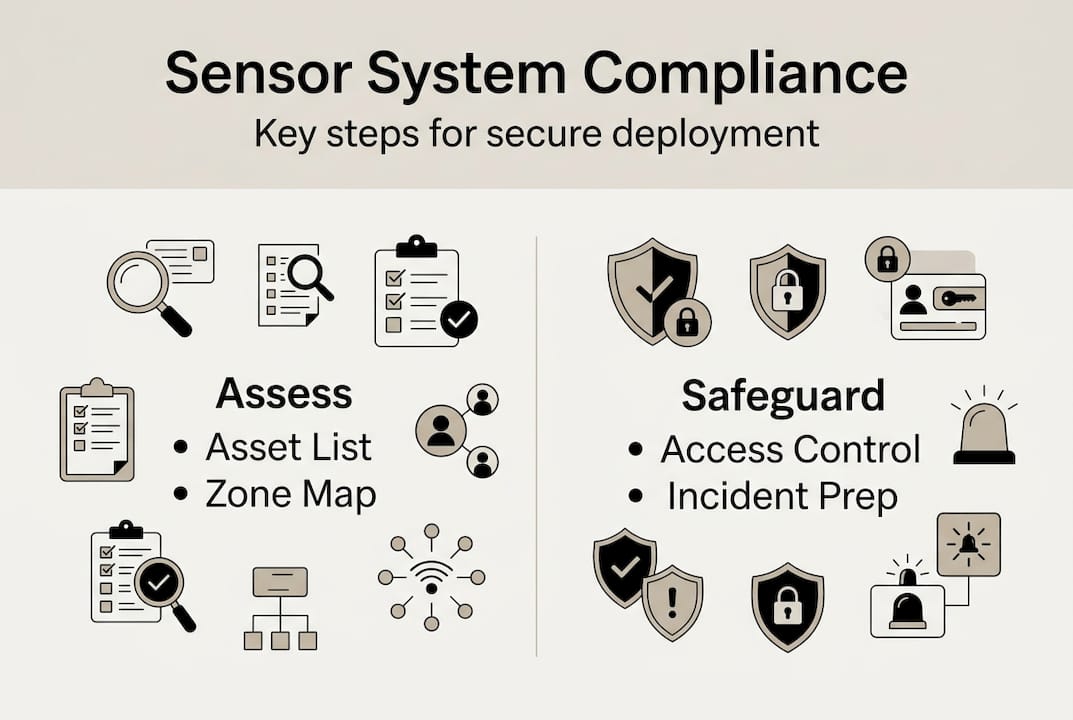
Step-by-step approach to security compliance for sensing systems
Now that you know the standards and mandates, here's a stepwise method you can actually operationalize.
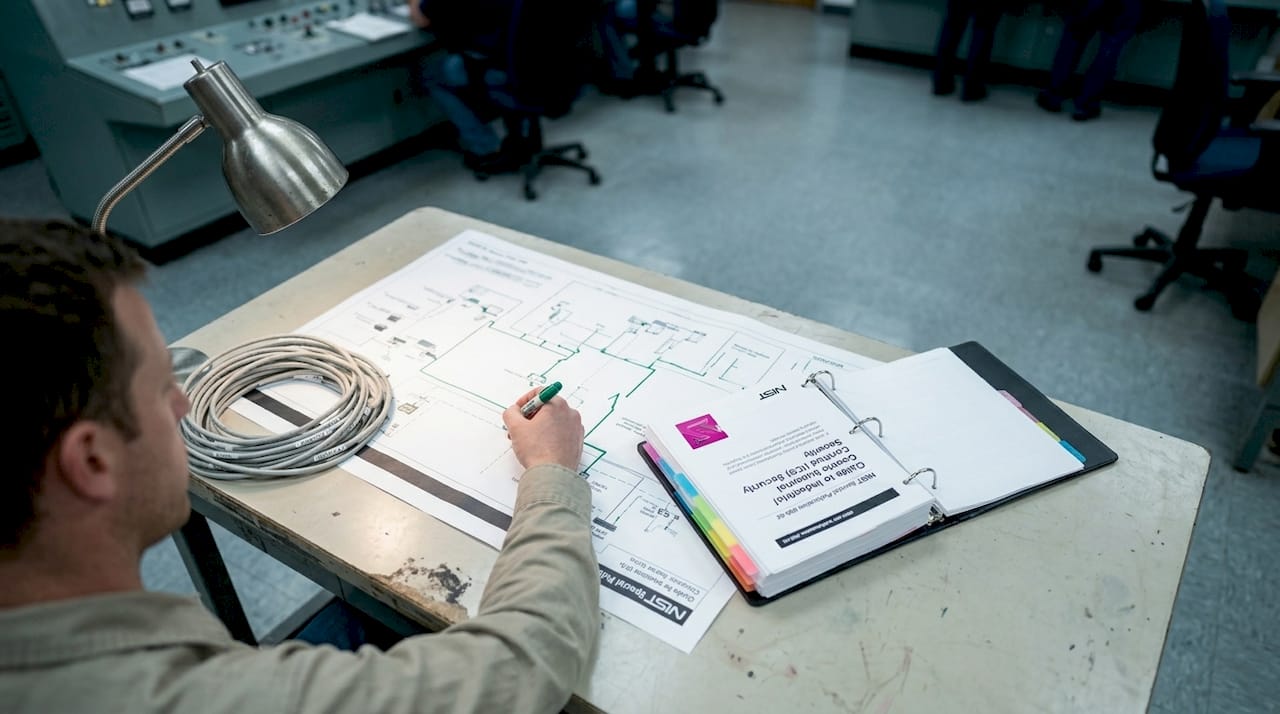
The zone/conduit model, risk assessment, and asset inventory form the backbone of any credible OT compliance program. Here is how to execute it:
-
Build a comprehensive asset inventory. Catalog every sensor, gateway, controller, and supporting OT/IT device. Include firmware versions, communication protocols, and physical locations. You cannot protect what you cannot see.
-
Map network zones and conduits. Define security zones based on risk level and criticality. Sensors connected to safety systems belong in higher-security zones than environmental monitors. Document conduits (communication paths) between zones.
-
Implement layered, defense-in-depth controls. Apply controls appropriate to OT environments: network segmentation, encrypted communications, role-based access, and physical tamper protection. Avoid applying IT-centric controls (like frequent reboots or aggressive patch cycles) that can disrupt OT availability.
-
Establish continuous monitoring and incident response. Align monitoring with CISA CPG practices. Define detection thresholds, escalation paths, and response playbooks specific to sensor anomalies and OT events.
-
Document and validate regularly. Maintain compliance records, conduct periodic audits, and test your controls through tabletop exercises or penetration testing scoped to OT environments. Regulators in Singapore and Vietnam increasingly expect documented evidence, not just verbal assurances.
Pro Tip: Zone and conduit modeling is the single highest-leverage step. It forces clarity on your attack surface, directly supports IEC 62443 compliance, and creates a foundation that scales as your sensor network grows. Pair this with sensor technology for automation insights to future-proof your architecture.
For a ready-to-use reference, the security safeguards checklist covers the core control categories aligned with these steps and the standards for security devices that apply to your hardware.
Common challenges and practical solutions
Even with a sound strategy, implementation challenges are common. Here's how to tackle the most pressing obstacles.
Legacy sensor systems are the most persistent barrier. Older sensors often lack encryption, use hardcoded credentials, or communicate over unencrypted protocols. Replacing them is ideal but rarely budget-feasible. The practical solution is risk-based segmentation: isolate legacy sensors in dedicated zones with strict conduit controls, and layer compensating controls (monitoring, physical access restrictions) around them.
High-security sensors must meet false alarm rates, tamper resistance, and other specifications, and legacy system integration brings unique risks that standard IT assessments often miss. Fiber optic and vibration sensors used in military perimeters or critical national infrastructure add another layer of complexity, with national-level specifications that may go beyond IEC 62443.
OT/IT convergence is another minefield. Many organizations apply IT-centric controls to OT sensor systems, inadvertently creating availability risks. An aggressive patch schedule that works fine for office laptops can take a production sensor network offline.
Key pain points and remediation strategies:
- Legacy sensor integration: Isolate in dedicated zones, apply compensating controls, document residual risk
- OT/IT protocol mismatch: Use protocol-aware firewalls and gateways designed for OT environments
- Vendor compliance gaps: Require IEC 62443 certification or documented security testing from hardware suppliers
- Insufficient documentation: Automate asset discovery and compliance logging where possible
- Cross-border regulatory differences: Use IEC 62443 as the common baseline, then layer local requirements on top
"The facilities that achieve compliance fastest are those that engage their system integrators and hardware vendors in the compliance process from day one, not after deployment."
Pro Tip: Engage system integrators early in any legacy upgrade project. Experienced integrators understand both the technical and regulatory constraints, and they can identify compliance risks during design that would be far more expensive to fix post-installation. Explore tailored security solutions that account for your specific sensor environment and regulatory context.
For additional context on integration for complex environments, system integration for public safety provides useful perspective on how integration decisions affect long-term compliance outcomes.
Why risk-based, OT-focused compliance trumps IT-first approaches
Having explored the mechanics and pitfalls, it's vital to rethink your compliance mindset itself.
The most common mistake we see across Southeast Asian facilities is applying IT security frameworks wholesale to OT sensor environments. IT frameworks prioritize confidentiality. OT environments prioritize availability and physical safety. When you force an IT-first model onto a sensor network, you end up with controls that look good on paper but create real operational risk.
The regulatory momentum across the region confirms this. Vietnam's QCVN 135 and Singapore's CSA advisories both reflect OT-aware thinking, not generic IT checklists. The most successful deployments we've seen align with IEC 62443 and NIST SP 800-82 as the OT foundation, then layer local mandates on top as targeted additions.
Our position is direct: don't wait for enforcement to drive your compliance program. Build OT-aligned compliance into your sensor systems from the procurement stage. Tailored sensor compliance designed around your actual risk profile will always outperform a generic IT checklist applied retroactively. The facilities that do this well are not just compliant. They are operationally stronger, more resilient, and better positioned for the next wave of regulatory requirements.
How BeyondSensor helps you achieve compliance with confidence
If you're ready to turn these best practices into action, BeyondSensor stands ready to help.
BeyondSensor brings deep expertise in regulatory-aligned sensor security across Singapore, Malaysia, the Philippines, and expanding into Thailand and Vietnam. We design solutions that meet both international standards like IEC 62443 and local mandates like QCVN 135:2024/BTTTT, so your sensing infrastructure is built for compliance from day one.
Our team works directly with security agencies and government facilities to address the exact challenges covered in this guide: legacy integration, OT/IT convergence, zone modeling, and cross-border regulatory alignment. Explore our security system innovations to see how our sensing technologies are engineered for compliance and operational resilience. Visit BeyondSensor to connect with our regional experts and start building a compliance program that holds up under scrutiny.
Frequently asked questions
What is the most important security standard for sensor-based systems in industry?
IEC 62443 is the primary standard for industrial sensor-based systems, widely regarded as the top international cybersecurity framework due to its OT-centric approach and layered Security Level requirements.
How do Singapore and Vietnam regulate sensor security compliance?
Singapore's CSA issues ICS protection advisories covering segmentation and access controls, while Vietnam enforces QCVN 135:2024/BTTTT for sensors and IP cameras from 2026, mandating encryption, unique passwords, and firmware integrity verification.
What are the biggest challenges for legacy sensor system compliance?
Legacy sensors often lack modern security features like encryption or unique credentials, requiring risk-based segmentation and controls to achieve compliance without full replacement.
What are the key steps to achieve security compliance in sensor systems?
Asset inventory, risk-based zone segmentation, layered OT-appropriate defenses, continuous monitoring, and documented validation processes are the essential steps for sensor-based compliance programs.
Recommended
- Physical security compliance: standards and sensor tech guide | News | BeyondSensor
- Security compliance: why it matters and how to master it | News | BeyondSensor
- Why tailored security solutions outperform generic systems | News | BeyondSensor
- Essential security checklist for infrastructure: 18 safeguards | News | BeyondSensor
- Security Policy - CorpHedge - CorpHedge
Read More Articles

Top 4 Titan-SG.com Alternatives 2026
Discover 4 titan-sg.com alternatives for sensor-based security solutions and compare their features effectively.

Defining operational efficiency in security: insights & best practices
Learn how to define and measure operational efficiency in security with key metrics, benchmarks, and sensor strategies tailored for Southeast Asia agencies.

Top advantages of sensing solutions for secure facilities
Discover the top advantages of advanced sensing solutions for security and operational efficiency in Southeast Asian industrial and smart infrastructure facilities.

Top intelligent sensing technologies to boost facility security
Discover top intelligent sensing technologies for facility security in 2026. Compare AI video analytics, environmental sensors, and access control solutions.
Let's Build YourSecurity Ecosystem.
Whether you're a System Integrator, Solution Provider, or an End-User looking for trusted advisory, our team is ready to help you navigate the BeyondSensor landscape.
Direct Advisory
Connect with our regional experts for tailored solutioning.