
Learn how to upgrade physical security workflows with advanced sensor solutions. A step-by-step guide for security managers and facility owners in Southeast Asia.

Optimize physical security workflows with advanced sensors

TL;DR:
- Sensor integration automates and accelerates physical security workflows, reducing human error.
- Proper facility assessment, planning, and validation are crucial for effective sensor-based security upgrades.
- Southeast Asian facilities must redesign workflows first, then select tailored sensor solutions for optimal security.
Facility security teams across Southeast Asia are under pressure. Threats are evolving faster than legacy workflows can respond, and the cost of a missed detection is no longer just operational. It's reputational and financial. The physical security market is growing from USD 147B in 2024 to a projected USD 216B by 2030, driven by AI and sensor integration. That growth signals where the industry is heading. This guide walks security managers and facility owners through every stage of upgrading to sensor-driven workflows, from understanding the fundamentals to validating results in the field.
Table of Contents
- Understanding physical security workflows and sensor integration
- Preparing your facility for sensor-based workflow upgrades
- Implementing sensor-driven physical security workflows: Step-by-step process
- Validating, troubleshooting, and optimizing your security workflow
- Expert perspective: Why Southeast Asian managers must rethink security workflows now
- Enhance your security workflow with BeyondSensor solutions
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Sensor integration essentials | Sensor-based solutions vastly improve monitoring, detection, and response in facility security workflows. |
| Preparation is critical | Assessing facility needs and aligning hardware/software requirements set the foundation for successful upgrades. |
| Stepwise deployment | Follow clear installation and configuration steps to ensure optimal sensor coverage and functionality. |
| Continuous validation | Regular checks and workflow optimizations are necessary to maintain high-security standards. |
| Expert-driven innovation | Facility owners in Southeast Asia must embrace sensor-driven workflows for future-proof operational efficiency. |
Understanding physical security workflows and sensor integration
A physical security workflow is the structured sequence of actions your team follows to protect a facility. It covers everything from perimeter monitoring and access control to incident detection, escalation, and post-event reporting. When these steps are manual, siloed, or dependent on human attention alone, gaps appear. Threats slip through. Response times stretch.
The core workflow steps are straightforward: continuous monitoring, anomaly detection, alert generation, response dispatch, and documentation. In a traditional setup, each step depends heavily on personnel. A guard watches a monitor. A supervisor reviews logs. A report gets filed hours later. The chain is only as strong as its slowest human link.
Sensor integration changes this. Intelligent sensing technologies replace reactive human monitoring with proactive, automated detection. IoT sensors, thermal cameras, motion detectors, and access control nodes feed real-time data into a centralized platform. AI processes that data continuously, flagging exceptions and triggering automated responses before a human even sees the alert.
Video surveillance and sensor-based systems now lead physical security workflow improvement globally, with video surveillance holding over 50% of market share. This is not a trend. It is the new operational baseline.
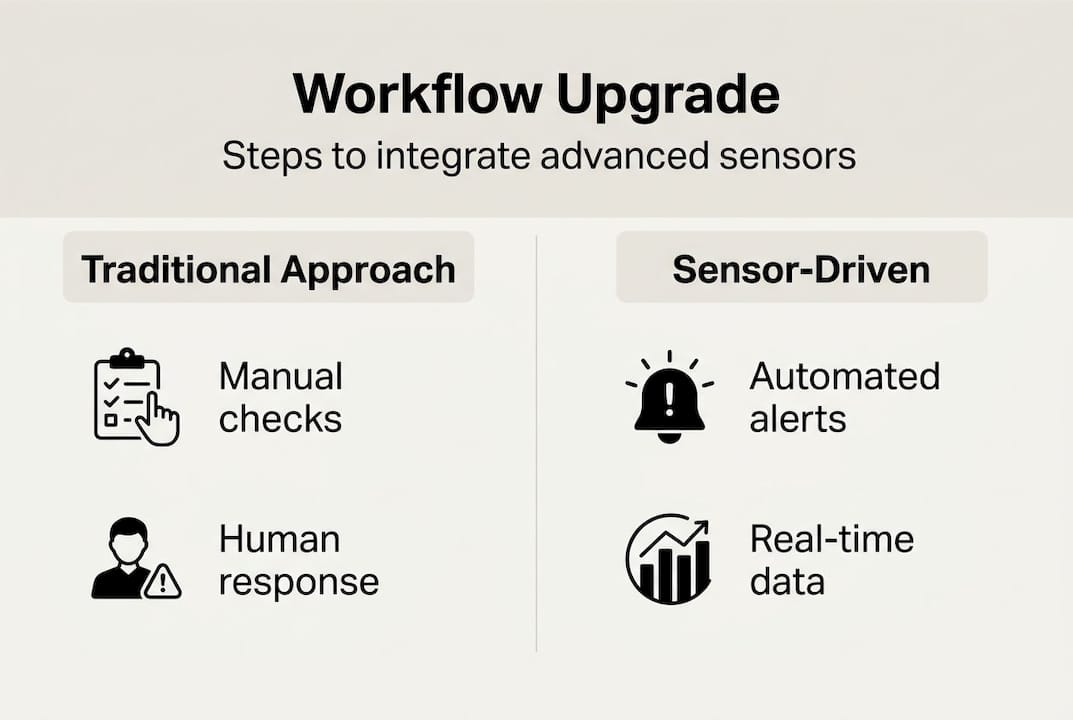
Here is how the two approaches compare:
| Workflow element | Traditional approach | Sensor-integrated approach |
|---|---|---|
| Monitoring | Manual, shift-dependent | Continuous, automated |
| Detection speed | Minutes to hours | Seconds |
| Alert accuracy | Variable, human error prone | High precision, AI-filtered |
| Documentation | Manual entry, delayed | Automated, real-time logs |
| Scalability | Limited by headcount | Scales with infrastructure |
The operational advantages of advanced sensing for security extend beyond speed. They include consistency, auditability, and the ability to correlate events across multiple zones simultaneously. For facility owners managing large or multi-site properties, this level of visibility is transformative.
Key capabilities enabled by sensor integration include:
- Real-time perimeter alerts triggered by motion, heat, or unauthorized access
- Cross-sensor event correlation that links related incidents across zones
- Automated escalation that routes alerts to the right responders instantly
- Audit-ready logs generated without manual input
This is the foundation your upgraded workflow will be built on.
Preparing your facility for sensor-based workflow upgrades
With a clear understanding of workflows, the next step is preparing your facility for an effective upgrade. Jumping straight to hardware procurement without a structured assessment is one of the most common and costly mistakes security managers make.
Start with a full facility audit. Walk every zone, identify existing equipment, and map your current workflow steps. Note where detection gaps exist, where response times are slowest, and where your team relies most on manual processes. This audit becomes your integration roadmap.

AI and IoT sensors are reshaping security infrastructure across Southeast Asia, and facilities that skip this preparation phase often end up with fragmented systems that do not communicate effectively. Compatibility between new sensors and your existing infrastructure is non-negotiable.
Here is a comparison of legacy versus sensor-based solutions to help frame your assessment:
| Factor | Legacy systems | Sensor-based solutions |
|---|---|---|
| Data output | Periodic, manual | Continuous, automated |
| Integration capability | Limited, proprietary | Open APIs, IoT-ready |
| Maintenance burden | High, reactive | Predictive, lower cost |
| Compliance readiness | Manual documentation | Built-in audit trails |
| Scalability | Difficult | Modular and flexible |
Follow these steps before committing to any hardware or software purchase:
- Map your current workflow end to end, including all handoff points between teams.
- Identify integration requirements for your existing access control, CCTV, and alarm systems.
- Define performance benchmarks such as target detection speed and false alarm thresholds.
- Assess network infrastructure to confirm bandwidth and connectivity support sensor data loads.
- Review compliance obligations relevant to your jurisdiction and industry sector.
For sensor security tips specific to compliance and safety, consult regional guidelines early in the planning phase. Retrofitting for compliance after installation is expensive.
Pro Tip: Before finalizing your sensor selection, request a compatibility validation from your vendor. Many facilities in Southeast Asia run mixed-generation infrastructure, and assuming interoperability without testing it is a fast path to integration failure. Tailored security solutions consistently outperform off-the-shelf systems precisely because they account for these variables upfront.
Implementing sensor-driven physical security workflows: Step-by-step process
Once preparations are in place, effective implementation depends on precise execution. Rushing deployment to meet a deadline is how coverage gaps and configuration errors get locked into your workflow.
Follow this deployment sequence for best results:
- Install perimeter sensors first. Establish your outer detection boundary before addressing interior zones.
- Connect sensors to your central management platform and confirm data feeds are active and correctly labeled.
- Configure detection parameters for each sensor type, including sensitivity thresholds and exclusion zones.
- Set up automated alert rules that define escalation paths based on event type and severity.
- Integrate with existing access control and CCTV systems to enable cross-platform event correlation.
- Run a full simulation of your detection and response workflow before going live.
Sensor-based security workflows boost operational efficiency and response speed significantly when configured correctly. The simulation step is where most teams discover misconfigured thresholds or alert routing errors before they become real incidents.
Critical operational check: Before activating automated response protocols, verify that all alert escalation paths have been tested with live personnel. An automated system that routes alerts to an unmanned channel provides zero operational value. Confirm every handoff point in your response chain is staffed and acknowledged.
Pro Tip: Sensor placement is not just about coverage area. It is about sightlines, environmental interference, and traffic patterns. In Southeast Asian facilities, high humidity, reflective surfaces, and dense foot traffic can all affect sensor accuracy. Review the advantages of sensing solutions for placement guidance specific to high-density environments. For industrial sites, sensor technology in automation offers additional configuration best practices worth reviewing.
Document every configuration decision during deployment. When you need to troubleshoot or scale later, this record is invaluable.
Validating, troubleshooting, and optimizing your security workflow
With an operational workflow, the final stage is ensuring its effectiveness and adapting for future risks. Deployment is not the finish line. It is the starting point for continuous improvement.
Begin with a structured validation process. Test every sensor zone, every alert rule, and every escalation path. Use realistic scenarios that reflect actual threat types your facility faces, not just generic test cases.
Common workflow mistakes that undermine performance include:
- Skipping post-deployment validation, leaving misconfigured sensors undetected
- Over-relying on default alert thresholds without calibrating for your specific environment
- Failing to update response protocols after personnel or layout changes
- Neglecting firmware and software updates that affect sensor accuracy and security
- Ignoring false alarm data, which is a direct signal that thresholds need recalibration
Verification and optimization are essential to maximize the return on your sensor investment. A workflow that was accurate at launch will drift without active management.
Use these optimization strategies to maintain peak performance:
- Schedule quarterly sensor audits to check calibration, placement, and firmware status.
- Analyze false alarm rates monthly and adjust detection parameters accordingly.
- Review incident logs to identify patterns that suggest coverage gaps or response delays.
- Update escalation protocols whenever team structures or shift schedules change.
- Benchmark against security compliance standards to ensure your workflow meets current regulatory requirements.
Use a structured security checklist to formalize your validation cycle. For teams navigating regulatory requirements, following security compliance steps ensures your documentation holds up during audits. Optimization is not a one-time task. It is a discipline that separates high-performing security operations from those that are perpetually reactive.
Expert perspective: Why Southeast Asian managers must rethink security workflows now
Here is an uncomfortable truth: most facilities in Southeast Asia are not behind on technology. They are behind on workflow design. You can install the most advanced sensors available and still operate a fundamentally broken process if the workflow around those sensors has not been redesigned.
Rapid urbanization across the region is creating facilities that are larger, more complex, and more exposed than the workflows managing them were ever built to handle. Compliance demands from regulators in Singapore, Malaysia, and the Philippines are tightening. Threat landscapes are shifting toward sophisticated, multi-vector incidents that legacy detection logic simply cannot parse.
The managers who will lead this transition are not the ones buying the most hardware. They are the ones redesigning their processes first and selecting technology to fit those processes. Sensors are not a luxury upgrade. They are the operational infrastructure that modern facility security requires.
Tailored security solutions consistently outperform generic deployments because they are built around real workflow requirements, not vendor defaults. That distinction matters more in Southeast Asia than anywhere else, where environmental, regulatory, and operational variables are uniquely demanding.
Enhance your security workflow with BeyondSensor solutions
Upgrading your physical security workflow is a strategic decision, and the technology you choose should match the complexity of your environment.
BeyondSensor delivers high-precision, sensor-based security solutions purpose-built for Southeast Asian facilities. Whether you are a security agency scaling detection capabilities or a system integrator deploying multi-site infrastructure, our platform is designed to fit your workflow requirements. Explore security agency solutions or review options for system integrators to find the right fit. For cutting-edge detection and automation capabilities, the BeyondSecure innovation platform delivers the intelligent sensing infrastructure your upgraded workflow demands. Reach out to our regional team to start your assessment today.
Frequently asked questions
What is a physical security workflow?
A physical security workflow is a step-by-step process used to protect facilities from threats, covering monitoring, detection, alert generation, and response. The physical security market's growth is directly tied to sensor integration improving each of these steps.
How does sensor technology improve security operations?
AI and IoT sensors enable real-time detection and automated alerts, dramatically improving speed and accuracy compared to manual monitoring. They also generate audit-ready logs that support compliance and post-incident review.
What is the first step in upgrading to sensor-based workflows?
Start by auditing your current security process to map existing workflow steps and identify where detection gaps and response delays occur. This assessment determines which sensors are key to your specific integration points.
What are common mistakes when implementing sensor-driven workflows?
The most frequent errors include poor sensor placement, skipping post-deployment validation, and neglecting compliance guidelines. Optimization and verification after go-live are just as critical as the initial installation itself.
Recommended
- Top sensor security tips for safety & compliance 2026 | News | BeyondSensor
- Understanding advanced sensing: boost security and efficiency | News | BeyondSensor
- Top intelligent sensing technologies to boost facility security | News | BeyondSensor
- Top advantages of sensing solutions for secure facilities | News | BeyondSensor
Read More Articles

Top 4 Titan-SG.com Alternatives 2026
Discover 4 titan-sg.com alternatives for sensor-based security solutions and compare their features effectively.

Defining operational efficiency in security: insights & best practices
Learn how to define and measure operational efficiency in security with key metrics, benchmarks, and sensor strategies tailored for Southeast Asia agencies.

Top advantages of sensing solutions for secure facilities
Discover the top advantages of advanced sensing solutions for security and operational efficiency in Southeast Asian industrial and smart infrastructure facilities.

Top intelligent sensing technologies to boost facility security
Discover top intelligent sensing technologies for facility security in 2026. Compare AI video analytics, environmental sensors, and access control solutions.
Let's Build YourSecurity Ecosystem.
Whether you're a System Integrator, Solution Provider, or an End-User looking for trusted advisory, our team is ready to help you navigate the BeyondSensor landscape.
Direct Advisory
Connect with our regional experts for tailored solutioning.